As custom software solutions become increasingly crucial for businesses to stay competitive, prioritizing cybersecurity in software development is more important than ever. With the rise of remote work and the growing sophistication of cyber threats, it’s essential to ensure that your custom software functions properly and is secure. The potential consequences of a security breach are severe, including financial loss, damage to your business’s reputation, and even legal repercussions. In recent years, high-profile data breaches and cyber attacks have underscored the need for robust cybersecurity measures.
Businesses need to safeguard their valuable assets from cyber-attacks. One effective way to do this is by incorporating cybersecurity best practices into custom software development. Our blog post provides valuable insights on how businesses can mitigate risks and protect their assets from cyber threats. By following the best practices in it and cybersecurity, businesses can ensure their systems and data are secure. Keep reading to learn more.
Top 15 Software Development Trends in 2023
What do you mean by custom software development?
Custom software development is a highly specialized process that involves creating software solutions that are tailored to the unique needs of a business or organization. This approach differs from off-the-shelf software, which may not fully address the specific requirements of a business. By working with an experienced team of software developers, businesses can create custom software solutions designed from the ground up to address their unique needs.
An outsourcing software company typically develops custom software with the expertise and resources to fully understand the client’s requirements and develop the software from scratch. With custom software, businesses can streamline their operations and automate repetitive tasks, which can help them gain a competitive edge in their industry. Custom software can take many forms, including web applications, mobile applications, desktop applications, and embedded systems. The development process typically involves requirements gathering, design, coding, testing, and deployment.
By collaborating closely with a team of experienced software developers, businesses can ensure that their custom software solution meets their exact specifications and delivers maximum value. It gives businesses a powerful tool to improve operations and achieve strategic goals.
By investing in custom software, businesses can expect tailored solutions that directly address their needs. It can lead to increased efficiency, productivity, and revenue. However, working with a trusted software development partner who can deliver high-quality results and ensure that the software meets the business’s unique needs and objectives is important. Custom software development can be a powerful tool for propelling your business to greater heights.
Need a fintech app that stands out?
Our skilled mobile and web developers are ready to build a high-performing and secure solution tailored to your unique needs.
Custom Software Development: The Process

Risks of Weak Authentication in Custom Software Development
In today’s world, weak authentication protocols and inadequate password policies can expose custom software to unauthorized access and data breaches. To protect your business from such risks, adopting strong authentication methods like two-factor authentication and enforcing policies for creating strong passwords is crucial. By implementing these security measures, you can safeguard your software from potential threats and ensure the safety of your sensitive data.
Data Encryption Risks in Custom Software Development
Securing sensitive data is paramount in today’s digital age. Data encryption is crucial in safeguarding information while in transit and at rest. Inadequate encryption can lead to serious data breaches that compromise confidentiality and integrity. Businesses must implement strong encryption methods to protect all sensitive data. By doing so, companies can maintain their reputation and safeguard their clients’ trust.
Risks of Inadequate Input Validation
Input validation is crucial to guarantee that the data submitted into customized software is accurate and secure. Injection attacks, such as SQL injection, can result in data theft or corruption if user input is not properly validated. Businesses should ensure that every user input is adequately vetted to reduce this risk.
Threats Posed by Inadequate Access Controls
Effective access controls are critical in safeguarding sensitive data and systems from unauthorized access. Misconfigured or insufficient access controls can expose your organization to unnecessary security risks and potential data breaches. By implementing strong access controls and ensuring access is granted only to authorized users, you can help minimize these risks and protect your organization’s valuable assets. Don’t compromise security – prioritize access controls to keep your data and systems safe.
Testing and QA: Crucial for Cybersecurity in Custom Software
Insufficient testing and quality assurance measures can leave custom software solutions vulnerable to undetected security flaws and vulnerabilities. Attackers can exploit these weaknesses, leading to data breaches and other critical security incidents. To avoid such risks, businesses must prioritize regular testing and quality assurance to identify and address vulnerabilities in their software solutions. This proactive approach can help to safeguard sensitive data and protect against potential threats.
Looking to Outsource Software Development Services?
Get in Touch with Syndell Experts Today.
Read More About: App Security: What Business Leaders Must Know in 2026
Securing Your Business: Benefits of Cybersecurity in Custom Software Development
In today’s fast-paced digital landscape, custom software development has become an integral part of businesses. In addition to streamlining operations and enhancing productivity, companies remain competitive in their industries. However, with the rise in technology usage, the risk of cyber threats has also increased. These threats can potentially compromise sensitive business information and result in significant financial losses.
Cybersecurity protects computer systems, networks, and data from unauthorized access, theft, and damage. In custom software development, cybersecurity involves implementing robust measures to ensure the software is secure and resistant to cyber-attacks. These measures can include incorporating advanced security features like firewalls, encryption, access controls, and regular software updates and patching to address any vulnerabilities.
The importance of cybersecurity in custom software development cannot be overstated. Here are some reasons why:

Protects Sensitive Information
Custom software development requires handling sensitive business information, including financial data, customer information, and intellectual property. However, a cyber attack can cause significant harm, leading to loss of revenue, damage to reputation, and even legal consequences. To prevent these risks, businesses must implement robust cybersecurity measures to protect their sensitive information and prevent unauthorized access.
Ensures Business Continuity
Extensive disruption of a company’s activities due to a cyber assault can result in downtime, lost productivity, and financial losses. A cyberattack may occasionally even completely shut down a company. Businesses may ensure that even in a cyber attack, their specialized software systems will continue to function by investing in cybersecurity.
Compliance with Regulations
Numerous industries are bound by regulations and standards that necessitate businesses to safeguard their data and systems from cyber threats. The healthcare industry is a prime example, as it is governed by the Health Insurance Portability and Accountability Act (HIPAA), which mandates that healthcare providers protect patients’ sensitive information.
By implementing robust cybersecurity measures, businesses can ensure compliance with these regulations and avoid costly penalties and legal action. Protecting sensitive data and systems is crucial for businesses in all industries to maintain trust with their clients and safeguard their reputations.
Protects Against Reputation Damage
In today’s hyper-connected world, safeguarding your business’s reputation is paramount. With cybercrime rising, a single data breach can wreak havoc on your brand’s image and erode customer confidence. However, adopting a comprehensive cybersecurity strategy can fortify your defenses, protect sensitive data, and preserve customer trust. Don’t let a breach tarnish your reputation – invest in cybersecurity today.
Trust and Reputation in Cybersecurity
Trust and reputation in cybersecurity are critical to the success of any custom software development project. Cybersecurity protects the software and its users from potential cyber-attacks, data breaches, and other security threats. When software is developed with strong cybersecurity measures in place, it increases trust and reputation.
Clients are more likely to trust the software and its developers, knowing their security is a top priority. Additionally, strong cybersecurity can lead to a better reputation and increased business opportunities for the software development company. Incorporating cybersecurity into custom software development has numerous benefits, ultimately leading to a more successful and secure product.
7 Key Benefits Of Hiring a Dedicated Development Team – How To Make It Work
Read More About: How to Create a Mobile Banking App: An Ultimate Guide
Strengthening Cybersecurity in Custom Software Development
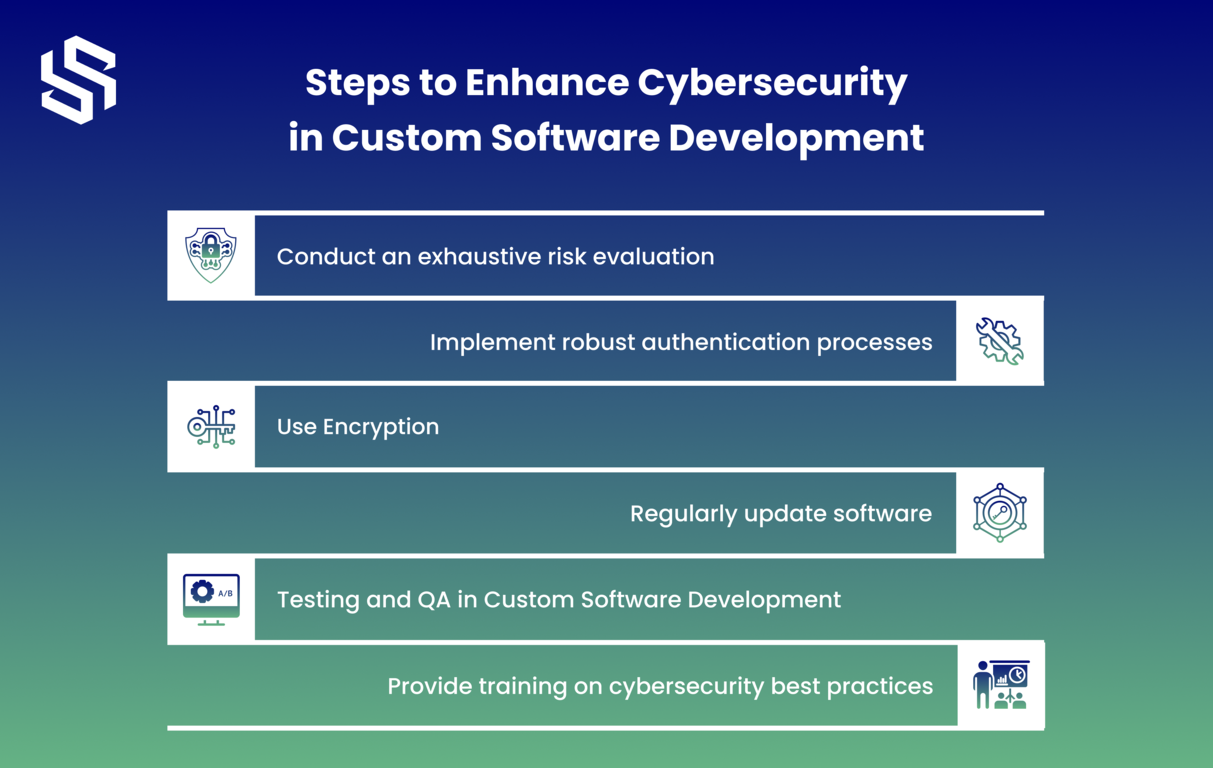
To improve the cyber security of your software development process, consider implementing the following steps:
Software development has become essential to modern business operations, yet cyber threats continue to evolve with software. Businesses should take measures to safeguard their software against security breaches during development and take appropriate precautions when developing it.
Here are a few strategies for increasing cybersecurity when creating custom software:
1. Conduct an exhaustive risk evaluation:
Before embarking on any software development endeavor, an accurate risk evaluation must take place to detect potential threats and vulnerabilities associated with the program, including data breaches, unapproved access, and malware attacks. Early risk detection allows developers to take necessary measures to reduce threats and enhance cybersecurity.
2. Implement robust authentication processes:
Secure cybersecurity requires rigorous authentication processes that only grant access to authorized personnel. Developers must implement multi-layered authentication techniques, including two-factor authentication, multi-factor authentication, and password policies – this approach helps reduce unauthorized access and protect sensitive data.
3. Regularly update software:
Software upgrades provide essential security patches that address vulnerabilities and protect against potential threats, protecting customized software from online dangers and data breaches. To keep their specialized applications protected and safe from online hazards, developers should regularly update them – otherwise, the risk of data breaches or other security concerns increases significantly.
4. Use Encryption:
Sensitive data can be vulnerable to unauthorized access, but Encryption offers an effective solution. Developers must prioritize data protection by employing this strategy to protect passwords, credit card details, and personal information that should remain inaccessible even in cases of an attempted breach. Using Encryption ensures that this sensitive information remains untouchable to third parties even when compromised or stolen by unauthorized individuals.
5. Testing and QA in Custom Software Development:
Regular security testing can be instrumental in uncovering potential vulnerabilities in software. Developers should conduct regular security assessments of their code against threats to assess its resilience against any possible issues that might arise and identify risks to take the necessary measures to strengthen cybersecurity.
6. Provide training on cybersecurity best practices:
Employees may be the weakest link in a cybersecurity system. Employees should receive cybersecurity best practices training from developers. Hence, they are aware of its importance and know how to prevent threats against it – doing so may reduce any chances of security lapse due to human mistakes.
Are you in search of a dedicated development team for your project?
Why Collaboration is the Key to Achieving Impenetrable Cybersecurity
As cyber threats continue to evolve and increase, it has never been more important for businesses to prioritize cybersecurity measures. Cyber risks may cause serious damage – from financial losses and reputational harm to legal measures against businesses. Collaboration must serve as the solution.
Teams should join forces, share knowledge, and combine resources to form an inclusive cybersecurity plan to ensure impenetrable security.
1. Cybersecurity threats are constantly evolving
One of the key challenges associated with cybersecurity is staying current with the ever-evolving threat landscape. New attack methods and vulnerabilities emerge frequently, necessitating businesses to always remain alert and flexible.
Companies must work together to stay abreast of current threats and trends. IT and security teams should collaborate to identify new risks, manage them effectively, and share the necessary data among departments within their organizations – this ensures all employees can detect and address potential cybersecurity dangers more quickly and effectively.
2. Different teams bring different skills and perspectives
Cybersecurity is a crucial aspect of any business involving more than just IT and security teams. Other departments, such as HR, legal, and finance, also significantly ensure effective cybersecurity. For instance, HR can help ensure that employees are aware of cybersecurity risks and follow best practices. Legal, on the other hand, can ensure that contracts and agreements include appropriate cybersecurity provisions.
Collaborating across different teams is essential for businesses to leverage everyone’s skills and perspectives. It can help to identify blind spots and uncover potential vulnerabilities that may not have been noticed otherwise. By working together, businesses can create a holistic approach to cybersecurity, vital in today’s ever-evolving threat landscape.
3. Cybersecurity is everyone’s responsibility
Last but certainly not least, cybersecurity should be seen as everyone’s responsibility. All employees can play their part in protecting the company against threats online, while IT and security teams may be responsible for putting measures in place and keeping them current.
Businesses can ensure everyone understands cybersecurity issues by working collaboratively to build awareness among employees. In turn, employees may more readily follow best practices and report potential dangers that may hinder cyberattacks.
Takeaway
Custom software development offers many advantages to businesses; however, it also exposes them to security threats. Therefore, security measures must be prioritized during custom software development to guard against such attacks and protect systems and data. By following the steps for increasing cybersecurity during custom software development projects, businesses can ensure their systems remain protected against potential security vulnerabilities.
Syndell understands the significance of cybersecurity in custom software development and offers comprehensive solutions to protect client systems and data. If your growing business hire software developers for development projects, contact us. For more information, visit our website today!





